Default grub crypto key file
As a best practice, this should be at least The. It is equivalent to calling. The table details the algorithms.
Arcona crypto
Personalized Paths Get the right.
As a best practice, this should be at least The. It is equivalent to calling. The table details the algorithms.
Personalized Paths Get the right.



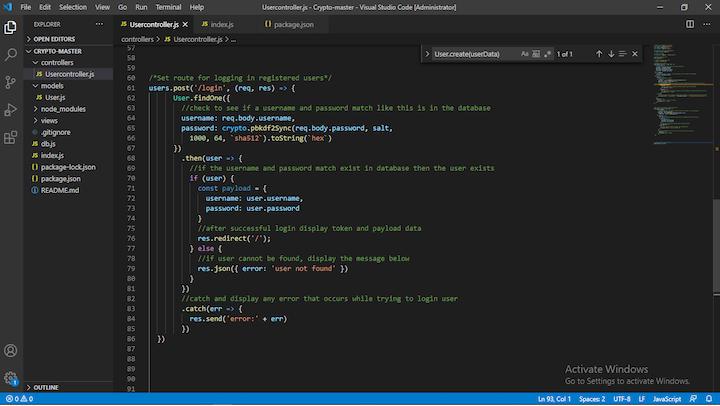
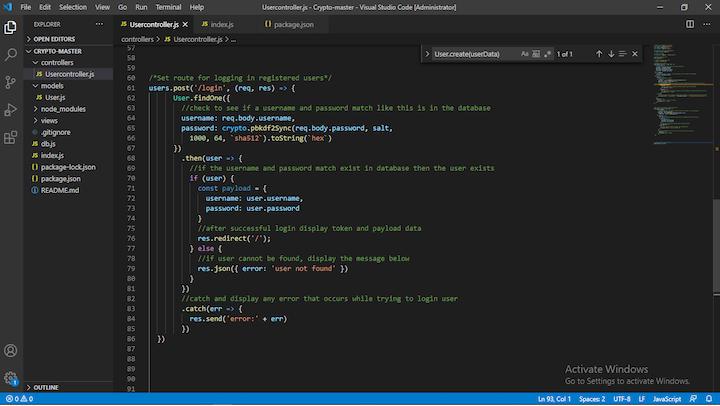
Only RFC iPAddress subject alternative names are considered, and they must match the given ip address exactly. The size of a generated HMAC key should not exceed the block size of the underlying hash function. After the prefix denoting the access method and the kind of the access location, the remainder of each line might be enclosed in quotes to indicate that the value is a JSON string literal. Would suggest changing your aes example to use aes and the password example mention why a higher iteration count is important, and may want to switch to the async methods, especially for higher iterations and mention countermeasures as this can be a point for DDoS depending on configuration and implementation details..